Learn and Practice Offensive and Defensive AI with Ease
Thursday, January 15th, 1:00 PM - 5:00 PM CT
TeamWorking, Chicago, IL
Join us, the winners of "Boss of the SOC 2025", for a practical, director-level workshop on how AI is being used by attackers and defenders — and how to prepare your security program today.
Only 30 seats available.
Your attackers are already using AI.
This workshop will teach you how you can respond.
AI isn't just hype anymore — it's a real problem. You already know the threat landscape has changed.
Attackers are using Generative AI to get around your defenses, run sophisticated phishing campaigns at scale, and automate attacks faster than your team can respond. The real question isn't whether you need to adapt — it's how quickly you can make it happen.
We made this workshop for the security leader who lives in both worlds — the Director who needs to brief the Board on AI risks, but also needs to understand exactly how an attacker exploits your M365 or AWS setup.
Learn and Practice Offensive and Defensive AI
-1.png?width=1645&height=1536&name=image%20(3)-1.png)
Part 1: AI for Offense (Red Teaming)
Phishing M365 with Data Exfiltration
- We simulate a live attack using AI. You'll see the attack path from the hacker's perspective — identifying gaps in Azure configurations that allowed the breach.
- Stop the attack with UnderDefense Agentic AI SOC and explore how telemetry correlation and 24/7 triage can stop attacks before they escalate.
Key takeaway: A BEC playbook, detection rules, and an MDR checklist tailored for phishing prevention.
Part 2: AI for Defense (Blue Teaming):
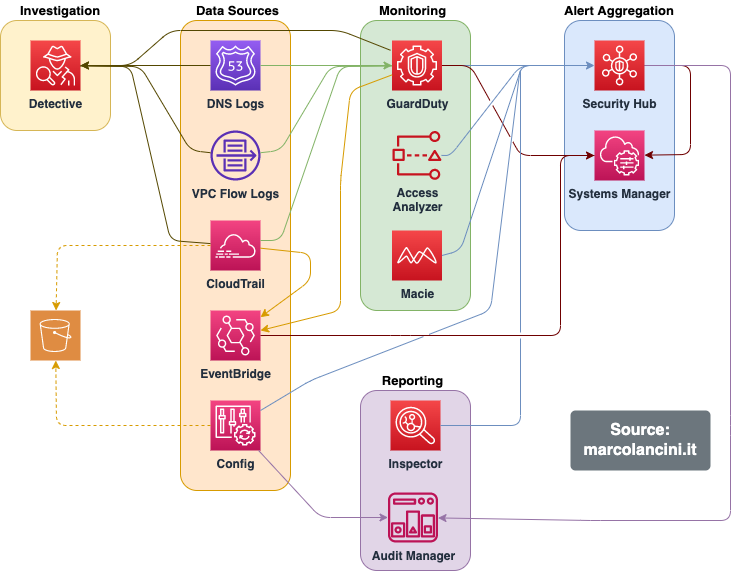
AWS Breach and Threat Hunting
- We will investigate a breach involving AWS EC2 autoscaling and detect threats in the cloud using Agentic AI SOC.
- You will learn how to use SIEM to uncover malicious activity, identify the attacker’s methods, and contain the breach.
Part 3: Simulation
Practical Hacking & Incident Response
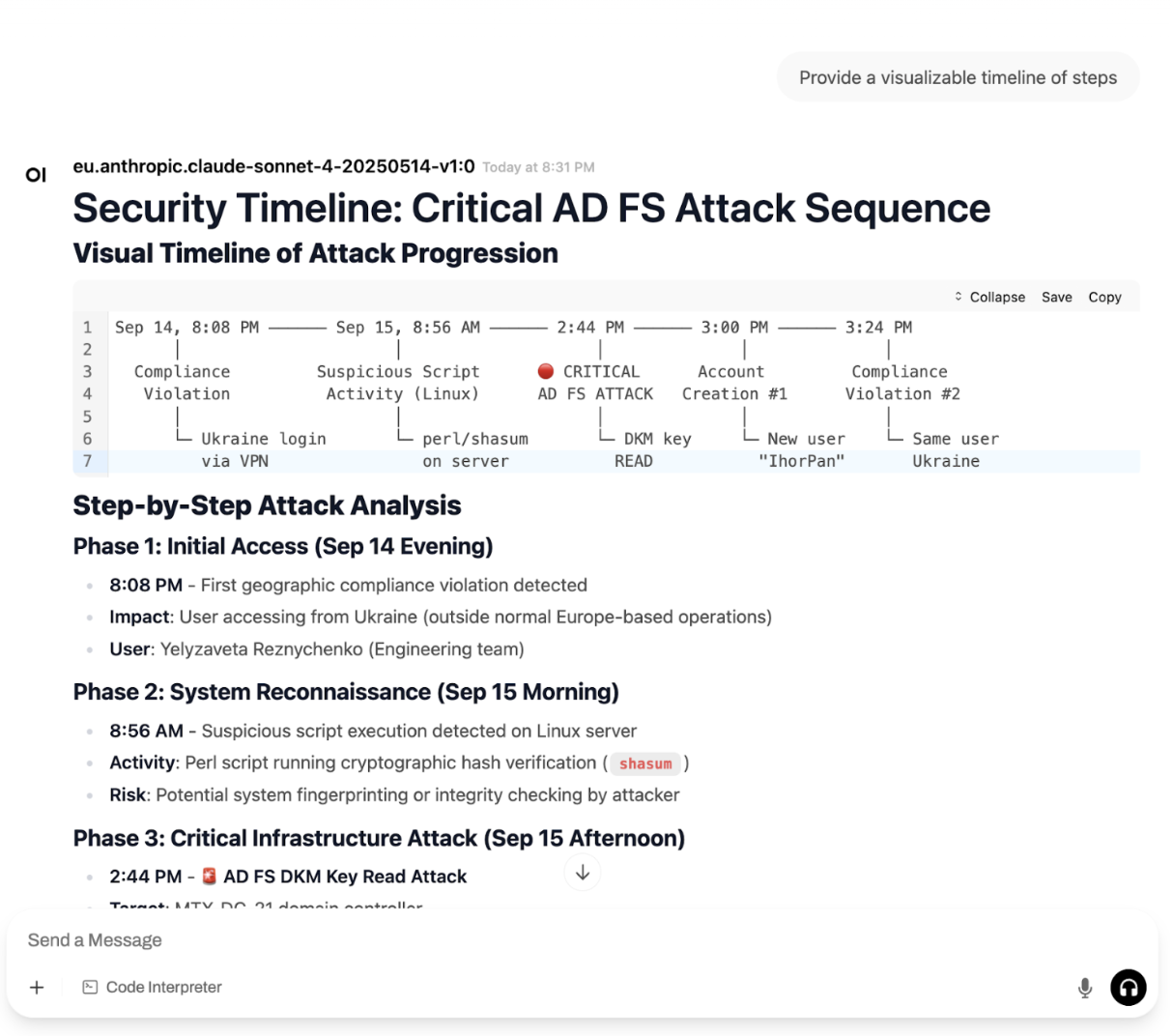
- Gain practical experience in hacking AD/Entra domains via leaked passwords, VPN access (via Fortinet), and domain takeover.
- Practice incident response by identifying patient zero, hunting the attack chain, and eradicating the threat from the network.
Get Practical Experience with Offensive & Defensive AI
Practical use of AI for Hacking
Experience real-world attack scenarios using both manual threat hunting and cutting-edge Agentic AI SOC technology to prevent breaches. Learn practical defense strategies against today's most sophisticated cyber threats.
Access to Threat Intel Platforms
Gain exclusive 1-month free access to Paranoid Labs, UnderDefense MAXI, and Alert Bars platforms. Put theory into practice with industry-leading tools designed to enhance your security operations immediately.
Threat Hunting: AI+Manual
Master advanced threat hunting techniques to proactively identify hidden adversaries in your network. Learn how AI augments human expertise to detect sophisticated threats before they cause damage.
AI for Incident Response
Walk away with a knowladge how to use AI playbook for practical phishing, identity, and cloud investigations. Apply these immediately to strengthen your organization's security posture.
Cloud & Identity Investigation
Develop practical skills to hunt in cloud environments for sophisticated attacks. Learn tactical approaches to secure these critical infrastructure components against emerging threats.
AI-Powered SOC Technology
Experience how AI-powered Security Operations Centers detect and respond to threats with unprecedented speed and accuracy. See firsthand how machine learning transforms alert triage and incident investigation.
SOC Checklist
Receive a SOC checklist that helps you evaluate and improve your organization's security operations. Identify gaps and implement best practices based on real-world security expertise.
Expert Networking Opportunity
Connect with industry experts and peers facing similar security challenges. Build valuable relationships while gaining insights from professionals with extensive experience combating advanced cyber threats.
Event Details
Date and time: January 15th, 1:00 PM - 5:00 PM CT
Venue: 20 N. Wacker Drive, 12th Floor
Chicago, IL 60606
View Location
What to take with you: Your laptop
The workshop is free of charge but requires registration


Reserve Your Spot for Hands-On AI Security Training
We Are Strategic
Security and Compliance Ally
Managed Detection and Response (MDR)
Stop threats in minutes, not days — 24/7 detection, response, and noise reduction across your entire environment.
AI SOC
AI-powered detection meets expert-led response. Professional incident handling, nonstop coverage, and faster recovery times.
Managed SIEM
Turn logs into action with continuous monitoring, custom tuning, and compliance-ready reporting — without the workload.
Penetration Testing
Validate your defenses with real-world red teaming. Uncover gaps, test detection capabilities, and prove your security stack works.
Cloud Detection & Response
Detect attacks and stop misconfigurations across Azure, AWS, GCP, and Kubernetes before disaster strikes.
Incident Response
Contain breaches fast with the right partner. Accelerate recovery, find root causes, and strengthen defenses for next time.
Compliance Automation
Pass audits with confidence. Streamlined SOC 2, ISO 27001, and HIPAA compliance without the manual overhead.
HackAI
Continuously Test your Perimeter defenses (EASA), find hidden gaps, unpatched and exploitable CVEs and strengthen before adversaries strike.
FAQ
What is this cybersecurity training about?
This half-day immersive cybersecurity training is designed for security professionals looking to enhance their defensive capabilities against AI-driven threats. You'll participate in hands-on exercises using both manual threat hunting techniques and cutting-edge Agentic AI SOC technology to detect, investigate, and respond to sophisticated cyber attacks. Our expert trainers will guide you through real-world attack simulations that demonstrate practical defense strategies.
Do I get access to security tools after training?
Yes! When you attend our training, you'll receive one month of complimentary access to three powerful security platforms: Paranoid Labs for advanced attack simulations, UnderDefense MAXI for mastering threat hunting and investigation tactics, and Alert Bars to improve your team's alerting and detection capabilities. These tools will allow you to immediately apply what you've learned and enhance your organization's security posture.
Who should attend this training event?
This training is ideal for CISOs, Security Directors, SOC Managers, and security professionals responsible for threat detection and response. While technical experience is beneficial, we've designed the training to accommodate various skill levels. The most important requirement is an interest in improving your organization's security operations and understanding how AI can enhance your defensive capabilities against evolving cyber threats.
What practical benefits will I gain from attending?
You'll leave with tangible assets including a BEC playbook, detection rules for phishing and identity attacks, MDR checklists, and incident response runbooks. More importantly, you'll gain practical experience with threat hunting, security investigation, and incident response that you can immediately apply in your organization. The hands-on nature of our training ensures you'll develop skills that directly translate to improved security operations.


